
[ad_1]

Getty Photographs
Hackers suspected of working for the Chinese language authorities are mass exploiting a pair of essential vulnerabilities that give them full management of digital personal community home equipment bought by Ivanti, researchers mentioned.
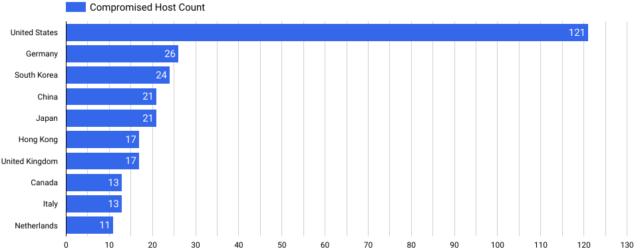
As of Tuesday morning, safety firm Censys detected 492 Ivanti VPNs that remained contaminated out of 26,000 units uncovered to the Web. Greater than 1 / 4 of the compromised VPNs—121—resided within the US. The three international locations with the following largest concentrations have been Germany, with 26, South Korea, with 24, and China, with 21.
Censys
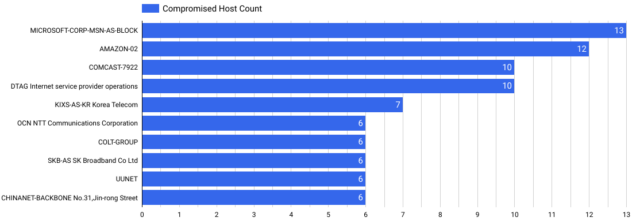
Microsoft’s buyer cloud service hosted essentially the most contaminated units with 13, adopted by cloud environments from Amazon with 12, and Comcast at 10.
Censys
“We performed a secondary scan on all Ivanti Join Safe servers in our dataset and located 412 distinctive hosts with this backdoor, Censys researchers wrote. “Moreover, we discovered 22 distinct ‘variants’ (or distinctive callback strategies), which may point out a number of attackers or a single attacker evolving their techniques.”
In an e mail, members of the Censys analysis group mentioned proof means that the folks infecting the units are motivated by espionage aims. That principle aligns with experiences printed lately by safety companies Volexity and Mandiant. Volexity researchers mentioned they think the menace actor, tracked as UTA0178, is a “Chinese language nation-state-level menace actor.” Mandiant, which tracks the assault group as UNC5221, mentioned the hackers are pursuing an “espionage-motivated APT marketing campaign.”
All civilian governmental businesses have been mandated to take corrective motion to stop exploitation. Federal Civilian Government Department businesses had till 11:59 pm Monday to comply with the mandate, which was issued Friday by the Cybersecurity and Infrastructure Safety Company. Ivanti has but to launch patches to repair the vulnerabilities. Of their absence, Ivanti, CISA, and safety firms are urging affected customers to comply with mitigation and restoration steering offered by Ivanti that embody preventative measures to dam exploitation and steps for patrons to rebuild and improve their techniques in the event that they detect exploitation.
“This directive isn’t any shock, contemplating the worldwide mass exploitation noticed since Ivanti initially revealed the vulnerabilities on January 10,” Censys researchers wrote. “These vulnerabilities are significantly critical given the severity, widespread publicity of those techniques, and the complexity of mitigation—particularly given the absence of an official patch from the seller as of the present writing.
When Avanti disclosed the vulnerabilities on January 10, the corporate mentioned it could launch patches on a staggered foundation beginning this week. The corporate has not issued a public assertion since confirming the patch was nonetheless on schedule.
VPNs are an excellent system for hackers to contaminate as a result of the always-on home equipment sit on the very fringe of the community, the place they settle for incoming connections. As a result of the VPNs should talk with broad components of the interior community, hackers who compromise the units can then broaden their presence to different areas. When exploited in unison, the vulnerabilities, tracked as CVE-2023-46805 and CVE-2024-21887, enable attackers to remotely execute code on servers. All supported variations of the Ivanti Join Safe—typically abbreviated as ICS and previously referred to as Pulse Safe—are affected.
The continued assaults use the exploits to put in a number of malware that acts as a backdoor. The hackers then use the malware to reap as many credentials as attainable belonging to varied staff and units on the contaminated community and to rifle across the community. Regardless of the usage of this malware, the attackers largely make use of an method referred to as “residing off the land,” which makes use of reliable software program and instruments so that they’re more durable to detect.
The posts linked above from Volexity and Mandiant present intensive descriptions of how the malware behaves and strategies for detecting infections.
Given the severity of the vulnerabilities and the results that comply with after they’re exploited, all customers of affected merchandise ought to prioritize mitigation of those vulnerabilities, even when which means briefly suspending VPN utilization.
[ad_2]