[ad_1]
An up to date model of an data stealer malware generally known as Jupyter has resurfaced with “easy but impactful adjustments” that goal to stealthily set up a persistent foothold on compromised programs.
“The group has found new waves of Jupyter Infostealer assaults which leverage PowerShell command modifications and signatures of personal keys in makes an attempt to cross off the malware as a legitimately signed file,” VMware Carbon Black researchers stated in a report shared with The Hacker Information.
Jupyter Infostealer, often known as Polazert, SolarMarker, and Yellow Cockatoo, has a observe file of leveraging manipulated SEO (search engine optimization) ways and malvertising as an preliminary entry vector to trick customers trying to find widespread software program into downloading it from doubtful web sites.
It comes with capabilities to reap credentials in addition to set up encrypted command-and-control (C2) communication to exfiltrate knowledge and execute arbitrary instructions.
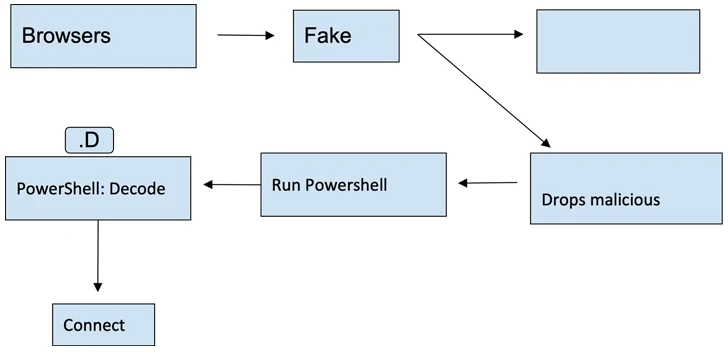
The most recent set of artifacts makes use of varied certificates to signal the malware to lend them a veneer of legitimacy, just for the faux installers to activate the an infection chain upon launch.
The installers are designed to invoke an interim payload that, in flip, employs PowerShell to hook up with a distant server and in the end decode and launch the stealer malware.
The event comes as stealer malware provided on the market on the cybercrime underground continues to evolve with new ways and methods, successfully decreasing the barrier to entry for lesser-skilled actors.
This consists of an replace to Lumma Stealer, which now incorporates a loader and the power to randomly generate a construct for improved obfuscation.
“This takes the malware from being a stealer sort to a extra devious malware that may load second-stage assaults on its victims,” VMware stated. “The loader offers a means for the risk actor to escalate its assault from knowledge theft to something as much as infecting its victims with ransomware.”
One other stealer malware household that has acquired regular enhancements is Mystic Stealer, which has additionally added a loader performance in latest variations to enrich its information-stealing skills.
“The code continues to evolve and develop the info theft capabilities and the community communication was up to date from a customized binary TCP-based protocol to an HTTP-based protocol,” Zscaler stated in a report late final month.
“The brand new modifications have led to elevated reputation with felony risk actors leveraging its loader performance to distribute extra malware households together with RedLine, DarkGate, and GCleaner.”
The continually evolving nature of such malware is additional exemplified by the emergence of stealers and distant entry trojans equivalent to Akira Stealer and Millenium RAT, which come fitted with varied options to facilitate knowledge theft.
The disclosure additionally arrives as malware loaders like PrivateLoader and Amadey have been noticed infecting hundreds of units with a proxy botnet dubbed Socks5Systemz, which has been round since 2016.
Cybersecurity agency Bitsight, which revealed particulars of the service final week, stated it recognized at the very least 53 servers associated to the botnet which can be distributed throughout France, Bulgaria, Netherlands, and Sweden.
The final word purpose of the marketing campaign is to flip contaminated machines into proxies able to forwarding site visitors for different actors, official or in any other case, as an extra layer of anonymity. It is suspected that the risk actors are of Russian origin, given the dearth of infections within the nation.
“The proxy service permits shoppers to decide on a subscription starting from $1 USD to $4,000 USD, payable in full utilizing cryptocurrency,” Bitsight stated. “Based mostly on community telemetry evaluation, it’s estimated that this botnet has roughly 10,000 contaminated programs with victims unfold throughout the globe.”
[ad_2]