[ad_1]
Cybersecurity researchers have developed a proof-of-concept (PoC) code that exploits a just lately disclosed vital flaw within the Apache OfBiz open-source Enterprise Useful resource Planning (ERP) system to execute a memory-resident payload.
The vulnerability in query is CVE-2023-51467 (CVSS rating: 9.8), a bypass for an additional extreme shortcoming in the identical software program (CVE-2023-49070, CVSS rating: 9.8) that might be weaponized to bypass authentication and remotely execute arbitrary code.
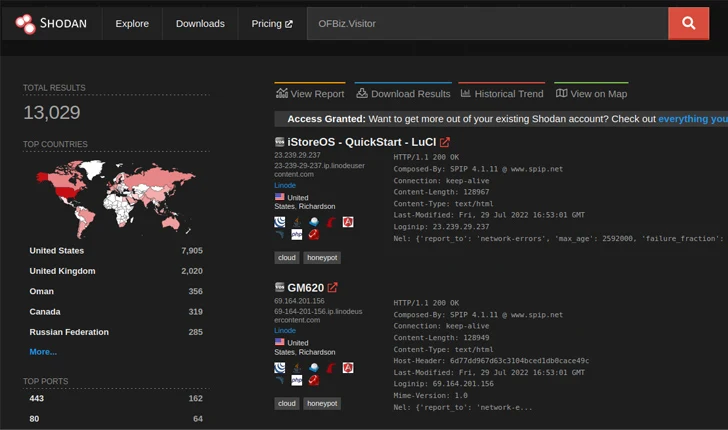
Whereas it was mounted in Apache OFbiz model 18.12.11 launched final month, risk actors have been noticed trying to take advantage of the flaw, concentrating on susceptible cases.
The most recent findings from VulnCheck present that CVE-2023-51467 will be exploited to execute a payload immediately from reminiscence, leaving little to no traces of malicious exercise.
Safety flaws disclosed in Apache OFBiz (e.g., CVE-2020-9496) have been exploited by risk actors prior to now, together with by risk actors related to the Sysrv botnet. One other three-year-old bug within the software program (CVE-2021-29200) has witnessed exploitation makes an attempt from 29 distinctive IP addresses over the previous 30 days, per knowledge from GreyNoise.
What’s extra, Apache OFBiz was additionally one of many first merchandise to have a public exploit for Log4Shell (CVE-2021-44228), illustrating that it continues to be of curiosity to each defenders and attackers alike.
CVE-2023-51467 is not any exception, with particulars a few distant code execution endpoint (“/webtools/management/ProgramExport”) in addition to PoC for command execution rising merely days after public disclosure.
Whereas safety guardrails (i.e., Groovy sandbox) have been erected such that they block any makes an attempt to add arbitrary internet shells or run Java code through the endpoint, the unfinished nature of the sandbox implies that an attacker may run curl instructions and acquire a bash reverse shell on Linux techniques.
“For a sophisticated attacker, although, these payloads aren’t preferrred,” VulnCheck’s Chief Know-how Officer Jacob Baines stated. “They contact the disk and depend on Linux-specific habits.”
The Go-based exploit devised by VulnCheck is a cross-platform answer that works on each Home windows and Linux in addition to will get across the denylist by profiting from groovy.util.Eval features to launch an in-memory Nashorn reverse shell because the payload.
“OFBiz is just not extensively fashionable, but it surely has been exploited prior to now. There’s a honest deal of hype round CVE-2023-51467 however no public weaponized payload, which known as into query if it was even potential,” Baines stated. “We have concluded that not solely is it potential, however we are able to obtain arbitrary in reminiscence code execution.”
[ad_2]



Keep up the amazing work!