[ad_1]

Latest variations of the Raspberry Robin malware are stealthier and implement one-day exploits which can be deployed solely on programs which can be vulnerable to them.
One-day exploits discuss with code that leverages a vulnerability that the developer of the impacted software program patched lately however the repair has both not been deployed to all shoppers or it has not been utilized on all weak programs.
From the second the seller discloses the vulnerability, which normally comes with publishing a patch, menace actors rush to create an exploit and use it earlier than the repair propagates to numerous programs.
In response to a report from Verify Level, Raspberry Robin has lately used no less than two exploits for 1-day flaws, which signifies that the malware operator both has the aptitude to develop the code or has sources that present it.
Raspberry Robin background
Raspberry Robin is a worm that Crimson Canary, a managed detection and response firm, first recognized in 2021. It spreads primarily via detachable storage gadgets resembling USB drives to determine a foothold on contaminated programs and facilitate the deployment of further payloads.
It has been related to menace actors like EvilCorp, FIN11, TA505, the Clop ransomware gang, and different malware operations, however its creators and maintainers are unknown.
Since its discovery, Raspberry Robin has repeatedly developed, including new options, evasion methods, and adopting a number of distribution strategies. One instance of evasion trick it applied was to drop pretend payloads to mislead researchers.
Verify Level reviews that it has noticed an uptick in Raspberry Robin’s operations beginning October 2023, with giant assault waves focusing on programs worldwide.
A notable swap in current campaigns is the usage of the Discord platform to drop malicious archive recordsdata onto the goal, seemingly after emailing the hyperlinks to the goal.
The archives comprise a digitally signed executable (OleView.exe) and a malicious DLL file (aclui.dll) that’s side-loaded when the sufferer runs the executable, thus activating Raspberry Robin within the system.
Concentrating on n-day flaws
When Raspberry Robin is first run on a pc, it would routinely try and elevate privileges on the machine utilizing quite a lot of 1-day exploits.
Verify Level highlights that the brand new Raspberry Robin marketing campaign leverages exploits for CVE-2023-36802, and CVE-2023-29360, two native privilege escalation vulnerabilities in Microsoft Streaming Service Proxy and the Home windows TPM Machine Driver.
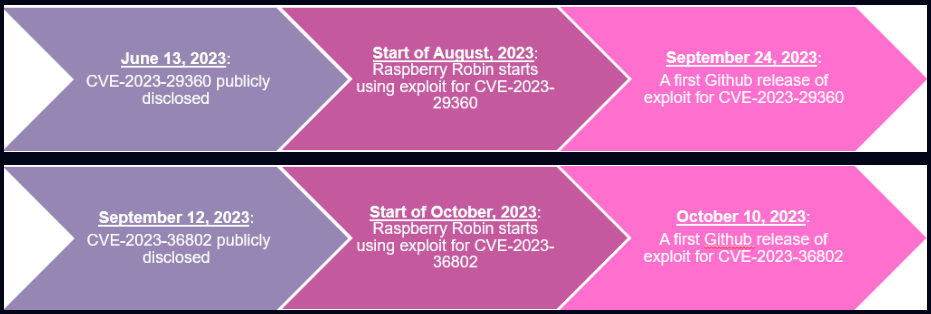
In each instances, the researchers say, Raspberry Robin began exploiting the issues utilizing a then-unknown exploit lower than a month after the safety points had been disclosed publicly, on June 13 and September 12, 2023.
As illustrated within the timeline diagram under, Raspberry Robin exploited the 2 flaws earlier than safety researchers first revealed proof of idea exploit code for the 2 flaws.
Particularly, concerning CVE-2023-36802, which permits attackers to escalate their privileges to the SYSTEM stage, Cyfirma reported that an exploit had been out there for buy on the Darkish Internet since February 2023, a full seven months earlier than Microsoft acknowledged and addressed the difficulty.
This timeline means that Raspberry Robin acquires 1-day exploits from exterior sources nearly instantly after their disclosure, as their value as zero days is probably going an excessive amount of even for bigger cybercrime operations.
Verify Level discovered proof that factors to this principle as effectively, because the exploits utilized by Raspberry Robin weren’t embedded into the primary 32-bit part, however deployed as exterior 64-bit executables, and in addition lack the heavy obfuscation usually seen with this malware.
New evasion mechanisms
Verify Level’s report additionally highlights a number of developments within the newest Raspberry Robin variants, which embrace new anti-analysis, evasion, and lateral motion mechanisms.
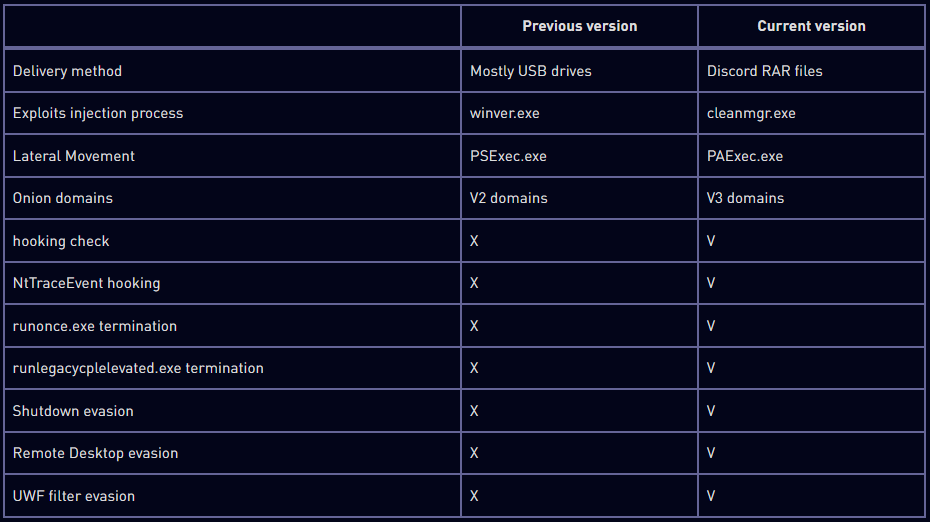
To evade safety instruments and OS defenses, the malware now makes an attempt to terminate particular processes like ‘runlegacycplelevated.exe,’ associated to Use Account Management (UAC), and patches the NtTraceEvent API to evade detection by Occasion Tracing for Home windows (ETW).
Furthermore, Raspberry Robin now checks if sure APIs, like ‘GetUserDefaultLangID’ and ‘GetModuleHandleW’, are hooked by evaluating the primary byte of the API perform to detect any monitoring processes by safety merchandise.
One other fascinating new tactic is the implementation of routines that use APIs like ‘AbortSystemShutdownW’ and ‘ShutdownBlockReasonCreate’ to stop system shutdowns that might interrupt the malware’s exercise.
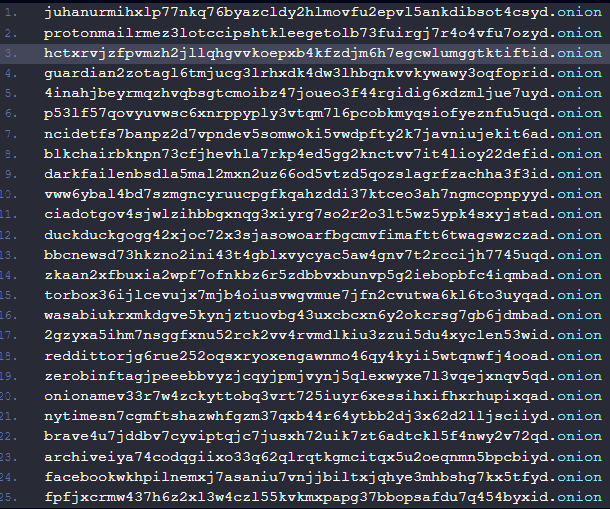
To hide the command and management (C2) addresses, the malware first randomly engages with one of many 60 hard-coded Tor domains pointing to well-known websites to make preliminary communications seem benign.
Lastly, Raspberry Robin now makes use of PAExec.exe as a substitute of PsExec.exe to obtain the payload immediately from the internet hosting location. This choice was seemingly made to extend its stealth, as PsExec.exe is understood to be misused by hackers.
The researchers imagine that Raspberry Robin will preserve evolving and add new exploits to its arsenal, in search of code that has not been launched publicly. Based mostly on observations in the course of the malware evaluation, it’s seemingly that the operators of the malware doesn’t create is related to a developer that gives the exploit code.
Verify Level’s report offers a listing of indicators of compromise for Raspberry Robin, which consists in hashes for the malware, a number of domains in the Tor community, and Discord URLs for downloading the malicious archive.
[ad_2]

