[ad_1]
The U.S. Justice Division (DoJ) on Friday introduced the seizure of on-line infrastructure that was used to promote a distant entry trojan (RAT) referred to as Warzone RAT.
The domains – www.warzone[.]ws and three others – have been “used to promote laptop malware utilized by cybercriminals to secretly entry and steal knowledge from victims’ computer systems,” the DoJ mentioned.
Alongside the takedown, the worldwide regulation enforcement effort has arrested and indicted two people in Malta and Nigeria for his or her involvement in promoting and supporting the malware and serving to different cybercriminals use the RAT for malicious functions.
The defendants, Daniel Meli (27) and Prince Onyeoziri Odinakachi (31) have been charged with unauthorized harm to protected computer systems, with the previous additionally accused of “illegally promoting and promoting an digital interception gadget and taking part in a conspiracy to commit a number of laptop intrusion offenses.”
Meli is alleged to have provided malware companies a minimum of since 2012 by means of on-line hacking boards, sharing e-books, and serving to different criminals use RATs to hold out cyber assaults. Previous to Warzone RAT, he had offered one other RAT generally known as Pegasus RAT.
Like Meli, Odinakachi additionally offered on-line buyer help to purchasers of Warzone RAT malware between June 2019 and no sooner than March 2023. Each people have been arrested on February 7, 2024.
Warzone RAT, also called Ave Maria, was first documented by Yoroi in January 2019 as a part of a cyber assault concentrating on an Italian group within the oil and gasoline sector in direction of the top of 2018 utilizing phishing emails bearing bogus Microsoft Excel recordsdata exploiting a identified safety flaw within the Equation Editor (CVE-2017-11882).
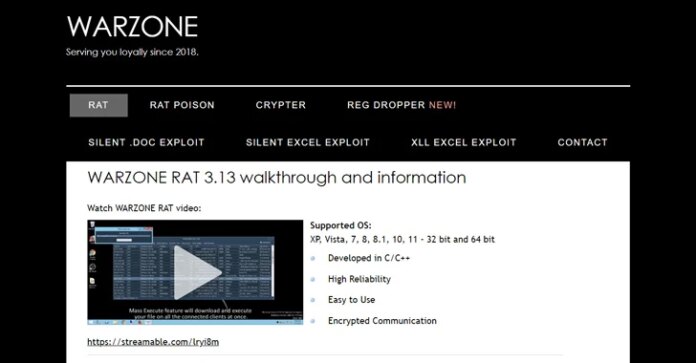
Offered below the malware-as-a-service (Maas) mannequin for $38 a month (or $196 for a 12 months), it capabilities as an info stealer and facilitates distant management, thereby permitting menace actors to commandeer the contaminated hosts for follow-on exploitation.
A few of the notable options of the malware embrace the power to browse sufferer file methods, take screenshots, report keystrokes, steal sufferer usernames and passwords, and activate the pc’s webcams with out the sufferer’s data or consent.
“Ave Maria assaults are initiated through phishing emails, as soon as the dropped payload infects the sufferer’s machine with the malware, it establishes communication with the attacker’s command-and-control (C2) server on non-HTTP protocol, after decrypting its C2 connection utilizing RC4 algorithm,” Zscaler ThreatLabz mentioned in early 2023.
On one of many now-dismantled web sites, which had the tagline “Serving you loyally since 2018,” the builders of the C/C++ malware described it as dependable and straightforward to make use of. In addition they offered the power for purchasers to contact them through electronic mail (solmyr@warzone[.]ws), Telegram (@solwz and @sammysamwarzone), Skype (vuln.hf), in addition to through a devoted “shopper space.”
A further contact avenue was Discord, the place the customers have been requested to get in contact with an account with the ID Meli#4472. One other Telegram account linked to Meli was @daniel96420.
Exterior of cybercrime teams, the malware has additionally been put to make use of by a number of superior menace actors like YoroTrooper in addition to these related to Russia over the previous 12 months.
The DoJ mentioned the U.S. Federal Bureau of Investigation (FBI) covertly bought copies of Warzone RAT and confirmed its nefarious capabilities. The coordinated train concerned help from authorities in Australia, Canada, Croatia, Finland, Germany, Japan, Malta, the Netherlands, Nigeria, Romania, and Europol.
[ad_2]